What goes into your scorecard?
By Jason Henson
On 20 December, 2021
Scorecards are a fundamental part of measuring performance and guiding activities and decision-making across an organization to drive business value. Your scorecard should tell a story and provide a framework for measuring your success.
The Jack of All Trades - What is it and do you need one?
By Phillip Everett
On 20 December, 2021
In the ever-changing landscape that is IT, there is a growing pressure to diversify skills. While organizations and people have varying degrees of success with this, the reason for that pressure is clear: teams need to be able to cover more ground with...
IT - What's your passion? Passion drives us!
By Jason Henson
On 20 December, 2021
What inspired you to get into IT in the first place? Was it the creative medium in code development? Was it the challenge of having something broken and fixing that problem so that you can save somebody’s day? Can you connect your passion in your career...
Loop1 Blog
Industry Tips, Tricks, and Latest News
By The Loopster
08 October, 2018
We live in a world these days where copy & paste is the shortest path to winning. In a world of Stack...
By The Loopster
10 April, 2018
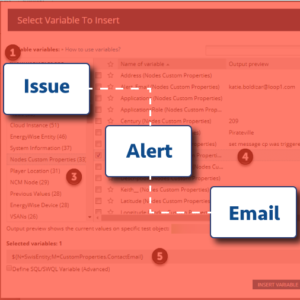
Loop1 Answers Top Questions from Alert Noise Webinar
We recently hosted a webinar on alert noise – the...


By The Loopster
15 March, 2018
When we started working with our client, he was overwhelmed.
He had finally convinced his organization...


By The Loopster
06 March, 2018
Ding. Buzz. New email in inbox. Ding, Ding, DING! What’s that noise? Yes, it’s another alert, most...


By The Loopster
29 January, 2018
Loop1 Systems is proud to be one of the selected SolarWinds partners to provide training for the SolarWinds...


By The Loopster
05 December, 2017
Co-Owner William Fitzpatrick Buys Out Partner, Assumes 100% Ownership
AUSTIN, Texas (Dec. 6, 2017) –...


By The Loopster
15 August, 2017
We’ve all been there. That same application admin has bonked his own server yet again. Only,...
By The Loopster
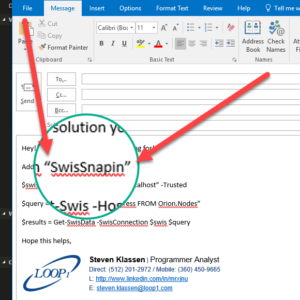
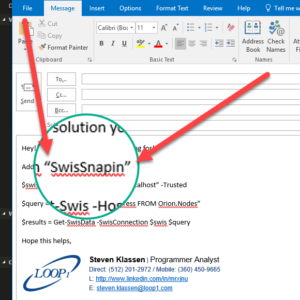
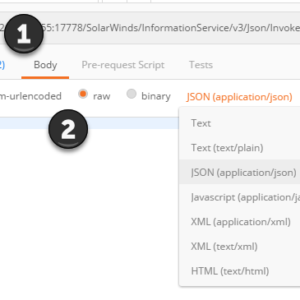
09 August, 2017
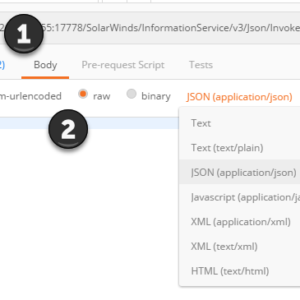
In the first post in this series, I started by going over authentication with the SolarWinds API and...


By The Loopster
31 July, 2017
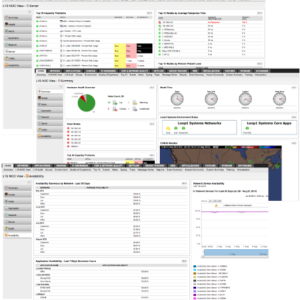
One of the things that is really great about Orion is that you can be up and running in under an hour...
No posts found