The Cost of a Cyber Attack
Around the world, more and more IT professionals are focusing on cybersecurity as safeguarding data is becoming increasingly more important to an organization’s internal success strategy. According to a study published by the Ponemon Institute in July of 2018, the average number of cybersecurity breaches increased by 6.4% in 2017 costing enterprise organizations an average of $3.86 million and 69 days from discovery to resolution of all breach-related issues. To get even more granular, organizations experienced an average per-record cost of $148 for every lost or stolen record. While US-based companies are the most vulnerable, both in the probability of an attack occurring and attack-related expenses, every domain across the globe is potentially at risk.
The good news? The IT industry as a whole is getting smarter and more well-prepared to guard against major attacks. Organizations are investing more in cybersecurity prevention with action items like:
- Purchasing software to ensure the safety and security of IT environments
- Employee Training
- Extensive use of encryption
- Creating reaction plans
- Assembling response teams to remediate issues as quickly as possible
“APPROXIMATELY $6 TRILLION IS EXPECTED TO BE SPENT ON CYBER SECURITY GLOBALLY BY THE YEAR 2021“
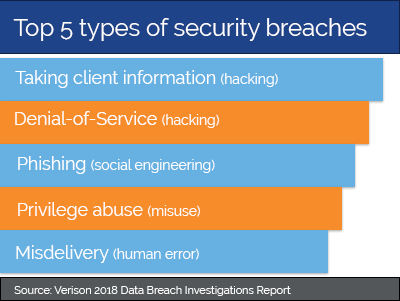
What are the most common types of breaches to occur?
It is an unfortunate reality that criminal activity exists in all facets of our society, including the IT industry. For many enterprise organizations, software solutions such as the SolarWinds security products are an important part of their security plan to keep their environments safe and protected from potential threats.
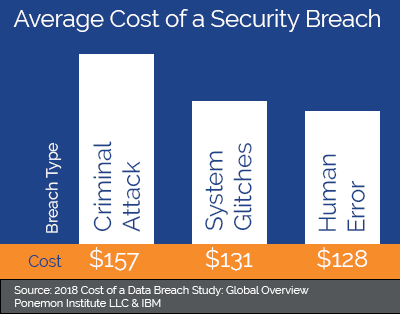
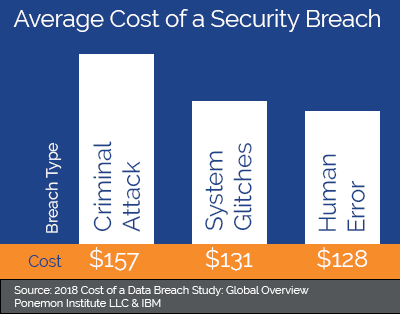
The three major contributors to cybersecurity breaches are criminal or malice attacks, system malfunctions, and human error, respectively.
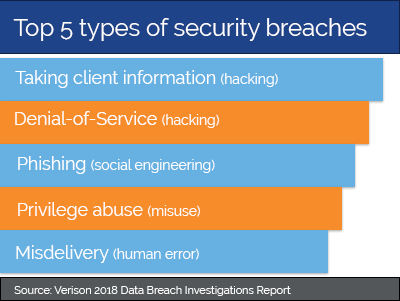
Security breaches can come in all sizes and with all different agendas. The most common type of breach usually involves hacking client data; however, there are many different motivators.
The “2018 Data Breach Investigations” by Verison cited more than 20 different types of security breaches or incidences as potential threats.
While hacking is the most common type of breach, the size for all breach types is getting bigger in terms of attack scope and the number of records affected.
The Identity Theft Resource Center (ITRC), reported a total of 1,632 data breaches and 197 million consumer records exposed in 2017—averaging 121,000 records per breach. In 2018, the ITRC reported a total of 1,244 breaches impacting over 446 million records.
An average of 358,000 records per breach in the US means there was an increase of nearly 66% of records impacted per incident in 2018.
The number of people exposed is even greater when you factor in other countries. According to Symantec’s “Norton Cyber Security Insights Report Global Results,” 978 million people in 20 countries were affected by cybercrime in 2017.
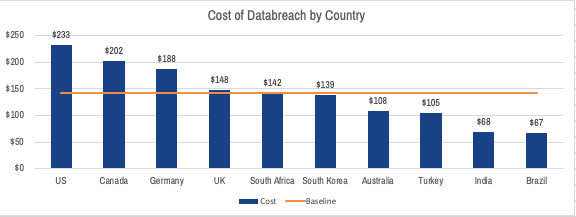
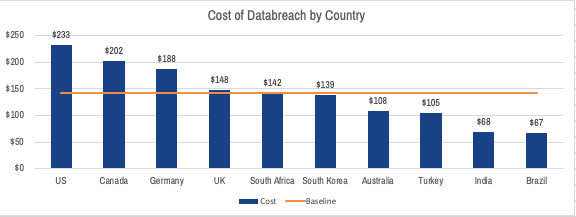
A major contributor to the significant cost difference among countries is the amount of money required to notify customers once a breach has occurred. Notification costs range widely throughout the world, due in large part to differences in regulation, with the United States being the highest at $740,000 as of 2018. In the United States, notification costs include:
- Creation of contact databases
- Determination of all regulatory requirements
- Engagement of outside experts
- Postal expenditures
- Email bounce-backs
- Inbound communication setups
The Real Cost of a Data Breach
As per IBM’s study, companies saved an average of $1 million when a security breach was discovered within 100 days of its intrusion and could save another $1 million if a breach was contained within 30 days. However, IBM’s study discovered it took approximately 197 days for a company to identify a breach and 69 days to contain the breach.
One of the largest security breaches in 2018, affecting approximately 383 million people globally, was the data breach at Marriott International. According to the ITRC, Marriott International’s network security was initially compromised in 2014, and the unauthorized access remained undiscovered and undisclosed until 2018.
These attacks can be detrimental to an organization’s bottom line, a lesson not lost on the global ride-share company, Uber. They learned of a database breach that impacted more than 600,000 customers worldwide in 2016 but waited to send breach notifications until almost a year later in 2017. US courts responded to these missteps by fining the organization over $148 million dollars (OAG-DC).
Other major breaches over the years such as Yahoo in 2013 affecting nearly all 3-billion Yahoo customers, and the infamous Equifax breach in 2017 impacting more than 146 million customers worldwide has led to major changes in legislation. By 2018, all 50 states had enacted some variation of data privacy laws while Europe went as far as passing the General Data Protection Rights Act (GDPR).
Tools like SolarWinds NetFlow Traffic Analyzer (NTA) and Server & Application Monitor (SAM) provide organizations of all sizes the ability to effectively monitor environments and detect possible threats earlier, saving time and money.
“GLOBAL AVERAGE COST PER PERSON OF A BREACH: $148“
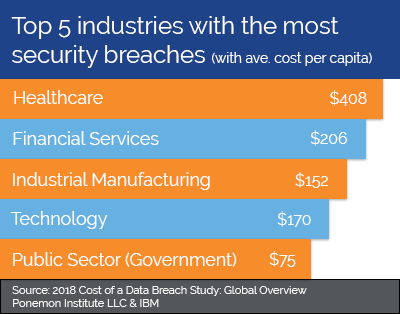
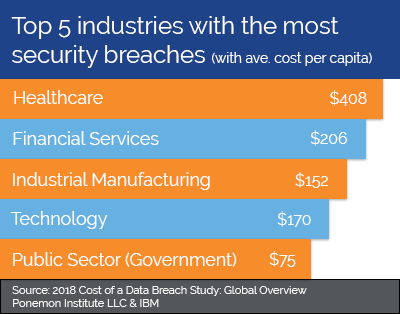
Due to the global nature of our society, all industries face challenges in maintaining a secure network. That being said, some industries face greater challenges in keeping data secure. Here are the top 5 industries most likely to encounter a breach along with the average cost per record:
- Healthcare = $408
- Financial Services = $206
- Technology = $170
- Industrial Manufacturing = $152
- Public Sector (Government) = $75
Networks for large, global businesses are not the only networks that get attacked; networks for small, local businesses are just as vulnerable. A report by Consumer Reports found that small businesses often have the same level of sensitive information but lack the knowledge or resources to maintain a secure network. “Cyber attacks are often automated, hitting many servers at once, and so hundreds of small businesses may get caught up for every 1 major company that’s affected.”
Regardless of the size of your organization, SolarWinds has solutions that can protect your IT environment from these types of attacks. Tools like Network Configuration Manager (NCM), Patch Manager, and Access Rights Manager can be used to satisfy controls and manager access rights, while Log & Event Manager (LEM) and Network Performance Manager (NPM) can be used to ensure that security controls are working properly.
Where do network security vulnerabilities come from?
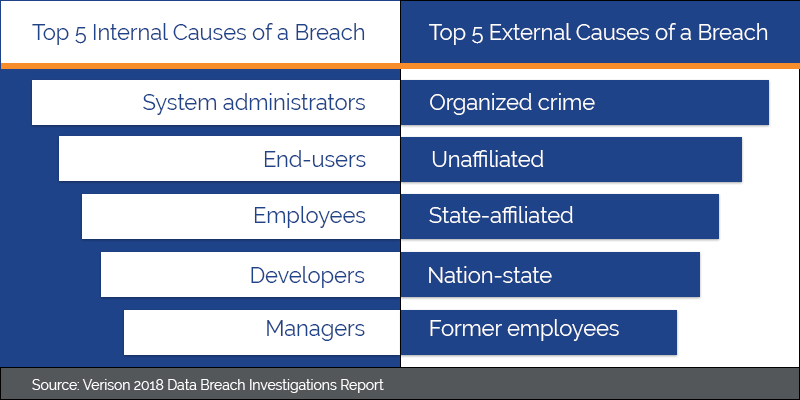
More often than not, security breaches are the result of outside entities wanting access to information on a network. But, threats to a network can also start from inside the network.
Unsurprisingly, there are many points of entry for malicious attackers to target your IT environment. According to the study published by Verison, these are the top 5:
- Web Applications
- Miscellaneous Errors
- Point of Sale
- Internet of Things (IoT) Devices
- Privilege Misuse
In their study, Verison found that web applications on a network were attacked more than any other point of entry. “This includes exploits of code-level vulnerabilities in the application as well as thwarting authentication mechanisms. of stolen credentials is still the top variety of hacking in breaches involving web applications, followed by SQLi.”
The Internet of Things: A Growing Threat
Additionally, Internet of Things (IoT) devices and other wireless devices are a growing area of concern. The OECD notes that the current consumer market (current employees using a network or the public accessing a network) regularly utilize a wide variety of IoT devices such as: wearables (smart watches, phones), smart home applications (Nest thermostats, TVs), and motor vehicles.
The increased number of IoT devices connecting to a network poses a number of threats to an organization’s IT environment. In the Federal Trade Commission’s (FTC) report “Internet of Things: Privacy & Security in a Connected World”, the FTC’s panel cautioned that many companies manufacturing IoT devices may not come from a background with network security in mind or are unfamiliar with security compliance.
Moreover, some low-end devices may not be able to update device software or, “may lack economic incentives to provide ongoing support or software security updates at all, leaving consumers with unsupported or vulnerable devices shortly after purchase.” According to the FTC, IoT devices could potentially:
- Allow for unauthorized access and misuse personal information
- Used to facilitate attacks on other systems
- Create safety risks that could be exploited to harm consumers
With the rising number of devices, it’s important to know who is on the network. SolarWinds’ Network Configuration Manager (NCM) can show what devices are connected, when devices approach end-of-service and end-of-life, make configuration changes, and even lock down devices with unauthorized access.
NCM’s network automation features were designed to manage changes across a network and maintain standards and service to all devices connected to the network all while reducing downtime and ensure that your network is compliant and secure.
“GROWING USE OF IoT DEVISES INCREASED THE AVERAGE COST PER PERSON PER BREACH BY $5“
While our ability to protect against attack continues to improve, IT trends confirm that the bad actors are just as adaptable. With every new software patch, there are numerous hackers ready and waiting to find new ways to exploit it.
The recent vulnerability discovered in Microsoft’s Remote Desktop Client serves as a good example of an organization taking a proactive approach to protecting customers once a threat was discovered. Microsoft went as far as offering a patch for XP clients, a product that had reached End of Service years before the vulnerability was discovered. While most individual users have moved on to newer versions of the product, Microsoft knew that many of their enterprise clients were running XP and did not want to risk exposing their systems to threat of attack.
This shift towards security preparedness should come as no surprise given the nearly $4 million price tag associated with identifying, containing, and remediating a data breach. Combine that with the potential of Federal prosecution and it would be downright reckless of organizations to exclude cybersecurity measures from their strategic plan. The growing number and size of attacks over the past decade confirm the importance of cybersecurity for all domains worldwide. As IT professionals it is our duty to remain diligent in our fight against attacks and continue to produce effective and innovative tools to protect the masses from the effects of a detrimental breach.
Do You Need Help Addressing Security Concerns?
Finding the right security strategy can be overwhelming. “What are my most vulnerable areas? What products are best for my environment? Where do I even begin?“ We get it. . .we have been there, and we want to help! Provide your contact details and a little bit of information about your environment and one of our team members will reach out to start the conversation.